Overview
Cyber security professionals need to create, analyse and test computer systems and networks to assure they will operate in the presence of attacks. In this unit, you will learn the types of attacks that may be encountered and the tools and techniques to prevent, detect and respond to those attacks. You will build your skills in virtualisation, cloud services and scripting to solve cyber security challenges. You will also learn special cyber security tools for detecting vulnerabilities, monitoring network traffic and responding to attacks.
Details
Pre-requisites or Co-requisites
Pre-Requisites: COIT11238 Networked Infrastructure Foundations AND COIT11222 Programming Fundamentals.
Important note: Students enrolled in a subsequent unit who failed their pre-requisite unit, should drop the subsequent unit before the census date or within 10 working days of Fail grade notification. Students who do not drop the unit in this timeframe cannot later drop the unit without academic and financial liability. See details in the Assessment Policy and Procedure (Higher Education Coursework).
Offerings For Term 1 - 2025
Attendance Requirements
All on-campus students are expected to attend scheduled classes - in some units, these classes are identified as a mandatory (pass/fail) component and attendance is compulsory. International students, on a student visa, must maintain a full time study load and meet both attendance and academic progress requirements in each study period (satisfactory attendance for International students is defined as maintaining at least an 80% attendance record).
Recommended Student Time Commitment
Each 6-credit Undergraduate unit at CQUniversity requires an overall time commitment of an average of 12.5 hours of study per week, making a total of 150 hours for the unit.
Class Timetable
Assessment Overview
Assessment Grading
This is a graded unit: your overall grade will be calculated from the marks or grades for each assessment task, based on the relative weightings shown in the table above. You must obtain an overall mark for the unit of at least 50%, or an overall grade of 'pass' in order to pass the unit. If any 'pass/fail' tasks are shown in the table above they must also be completed successfully ('pass' grade). You must also meet any minimum mark requirements specified for a particular assessment task, as detailed in the 'assessment task' section (note that in some instances, the minimum mark for a task may be greater than 50%). Consult the University's Grades and Results Policy for more details of interim results and final grades.
All University policies are available on the CQUniversity Policy site.
You may wish to view these policies:
- Grades and Results Policy
- Assessment Policy and Procedure (Higher Education Coursework)
- Review of Grade Procedure
- Student Academic Integrity Policy and Procedure
- Monitoring Academic Progress (MAP) Policy and Procedure - Domestic Students
- Monitoring Academic Progress (MAP) Policy and Procedure - International Students
- Student Refund and Credit Balance Policy and Procedure
- Student Feedback - Compliments and Complaints Policy and Procedure
- Information and Communications Technology Acceptable Use Policy and Procedure
This list is not an exhaustive list of all University policies. The full list of University policies are available on the CQUniversity Policy site.
Feedback, Recommendations and Responses
Every unit is reviewed for enhancement each year. At the most recent review, the following staff and student feedback items were identified and recommendations were made.
Feedback from Teaching Team Reflections
Some students have computers which have difficulty running the required virtual machines.
Transition from on-premise to cloud hosed virtual machines.
Feedback from Student Evaluations
Learning materials need to be improved.
Improve the learning materials, for example, by converting the practical exercises into self guided activities.
- Explain cyber security challenges and the technologies available to address those challenges
- Apply cyber security tools to identify vulnerabilities and protect computer systems
- Apply cloud services tools to automate common IT processes and task.
The Australian Computer Society (ACS) recognises the Skills Framework for the Information Age (SFIA). SFIA is adopted by organisations, governments and individuals in many countries and provides a widely used and consistent definition of ICT skills. SFIA is increasingly being used when developing job descriptions and role profiles. ACS members can use the tool MySFIA to build a skills profile.
This unit contributes to the following workplace skills as defined by SFIA 7 (the SFIA code is included)
- Information security (SCTY)
- Programming/software development (PROG)
- Security administration (SCAD)
- Penetration testing (PENT)
The National Initiative for Cybersecurity Education (NICE) Framework defines knowledge, skills and tasks needed to perform various cyber security roles. Developed by the National Institute of Standards and Technology (NIST), the NICE Framework is used by organisations to plan their workforce, including recruit into cyber security positions.
This unit helps prepare you for roles such as Systems Security Analyst, Network Operations Specialist and Systems Administrator, contributing to the following knowledge and skills:
- K0003 Knowledge of laws, regulations, policies, and ethics as they relate to cybersecurity and privacy.
- K0004 Knowledge of cybersecurity and privacy principles.
- K0005 Knowledge of cyber threats and vulnerabilities.
- K0006 Knowledge of specific operational impacts of cybersecurity lapses.
- K0040 Knowledge of vulnerability information dissemination sources (e.g., alerts, advisories, errata, and bulletins).
- K0044 Knowledge of cybersecurity and privacy principles and organizational requirements (relevant to confidentiality, integrity, availability, authentication, non-repudiation).
- K0071 Knowledge of remote access technology concepts.
- K0075 Knowledge of security system design tools, methods, and techniques.
- K0130 Knowledge of virtualization technologies and virtual machine development and maintenance.
- K0135 Knowledge of web filtering technologies.
- K0160 Knowledge of the common attack vectors on the network layer.
- K0274 Knowledge of transmission records (e.g., Bluetooth, Radio Frequency Identification (RFID), Infrared Networking (IR), Wireless Fidelity (Wi-Fi). paging, cellular, satellite dishes, Voice over Internet Protocol (VoIP)), and jamming techniques that enable transmission of undesirable information, or prevent installed systems from operating correctly.
- K0290 Knowledge of systems security testing and evaluation methods.
- K0297 Knowledge of countermeasure design for identified security risks.
- K0318 Knowledge of operating system command-line tools.
- K0339 Knowledge of how to use network analysis tools to identify vulnerabilities.
- S0031 Skill in developing and applying security system access controls.
- S0060 Skill in writing code in a currently supported programming language (e.g., Java, C++).
- S0073 Skill in using virtual machines. (e.g., Microsoft Hyper-V, VMWare vSphere, Citrix XenDesktop/Server, Amazon Elastic Compute Cloud, etc.).
- S0154 Skill in installing system and component upgrades. (i.e., servers, appliances, network devices).
- S0167 Skill in recognizing vulnerabilities in security systems. (e.g., vulnerability and compliance scanning).
Alignment of Assessment Tasks to Learning Outcomes
| Assessment Tasks | Learning Outcomes | ||
|---|---|---|---|
| 1 | 2 | 3 | |
| 1 - Online Quiz(zes) - 30% | |||
| 2 - Portfolio - 50% | |||
| 3 - Presentation - 20% | |||
Alignment of Graduate Attributes to Learning Outcomes
| Graduate Attributes | Learning Outcomes | ||
|---|---|---|---|
| 1 | 2 | 3 | |
| 1 - Communication | |||
| 2 - Problem Solving | |||
| 3 - Critical Thinking | |||
| 4 - Information Literacy | |||
| 5 - Team Work | |||
| 6 - Information Technology Competence | |||
| 7 - Cross Cultural Competence | |||
| 8 - Ethical practice | |||
| 9 - Social Innovation | |||
| 10 - First Nations Knowledges | |||
| 11 - Aboriginal and Torres Strait Islander Cultures | |||
Textbooks
There are no required textbooks.
IT Resources
- CQUniversity Student Email
- Internet
- Unit Website (Moodle)
- Suitable storage media, such as a removable USB 3.0 stick (≥128GB) for oncampus students without a laptop or as a fallback if you do not have enough harddrive space free
- Virtualbox (Version 7 or later)
- A computer with hardware resources suitable to run multiple virtual machines simultaneously, e.g. 12GB RAM, 128GB HDD free, Intel core i5 or above, Windows 7 or later.
All submissions for this unit must use the referencing style: Harvard (author-date)
For further information, see the Assessment Tasks.
j.shield@cqu.edu.au
Week 1
Begin Date: 10 Mar 2025Module/Topic
1 Introduction
Chapter
Refer to the unit website for the readings.
Chapter 6 of Hassell, J 2017, Learning PowerShell, Boston, DeG Press.
Events and Submissions/Topic
Week 2
Begin Date: 17 Mar 2025Module/Topic
2 Controls
Chapter
CIS Controls
Events and Submissions/Topic
Week 3
Begin Date: 24 Mar 2025Module/Topic
3 Threat Intelligence
Chapter
Chapter 3 of Thompson, E 2020, Designing a HIPAA-Compliant Security Operations Center, Apress L. P, Berkeley, CA.
Events and Submissions/Topic
Due A2 Reconnaissance (12.5%)
Portfolio Due: Week 3 Friday (28 Mar 2025) 11:45 pm AEST
Week 4
Begin Date: 31 Mar 2025Module/Topic
4 Vulnerabilities
Chapter
Chapter 4 of (Thompson 2020)
Events and Submissions/Topic
Week 5
Begin Date: 07 Apr 2025Module/Topic
5 Monitoring
Chapter
Chapter 5 of (Thompson 2020)
Events and Submissions/Topic
Due A2 Vulnerability detection (12.5%)
Vacation Week
Begin Date: 14 Apr 2025Module/Topic
No classes
Chapter
Events and Submissions/Topic
Week 6
Begin Date: 21 Apr 2025Module/Topic
6 Risks
Chapter
Chapter 1 of Bijalwan, A 2021, Network Forensics, CRC Press.
Events and Submissions/Topic
Week 7
Begin Date: 28 Apr 2025Module/Topic
7 Linux
Chapter
Chapters 6, 9, 10, 16, 17, 19, 20, 26-29 and 33 of Shotts 2019, The Linux Command Line.
Events and Submissions/Topic
Due A2 Internal attacks (12.5%)
Week 8
Begin Date: 05 May 2025Module/Topic
8 Attacks
Chapter
Chapter 3 of Garbis, J & Chapman, J 2021. Zero Trust Security, Apress.
Events and Submissions/Topic
Week 9
Begin Date: 12 May 2025Module/Topic
9 Cloud
Chapter
Chapter 1 of Collier, M & Shahan, R 2016, Foundations of Azure, 2nd edn, Microsoft.
Events and Submissions/Topic
Week 10
Begin Date: 19 May 2025Module/Topic
10 Python Scripting
Chapter
Chapters 2-11 of Severance, C 2016, Python for Everybody.
Events and Submissions/Topic
Due A2 Network attacks (12.5%)
Week 11
Begin Date: 26 May 2025Module/Topic
11 Presentations (tutorial only)
Chapter
Events and Submissions/Topic
Week 12
Begin Date: 02 Jun 2025Module/Topic
No classes
Chapter
Events and Submissions/Topic
Review/Exam Week
Begin Date: 09 Jun 2025Module/Topic
Chapter
Events and Submissions/Topic
Unit Coordinator: Jamie Shield, Cairns,
j.shield@cqu.edu.au,
Office: 07 4037 4750
1 Online Quiz(zes)
You will be assessed on background concepts in cybersecurity, networking, ICT and computer security technologies, offensive types of cybersecurity technologies, and applying defensive cybersecurity technologies. The quiz questions will involve short answer questions and activities such as writing shell commands and using cybersecurity tools.
10
Weekly
Week 12 Friday (6 June 2025) 11:45 pm AEST
Immediate feedback with grades subject to moderation.
This assessment consists of short answer questions and small activities such as the use of PowerShell, Bash and Python commands for scripting, network defense, monitoring and attacks. Each question will be marked according to the correctness of the answer, for example, successful use of commands to start a SYN flood attack.
- Apply cyber security tools to identify vulnerabilities and protect computer systems
- Apply cloud services tools to automate common IT processes and task.
2 Portfolio
You will create a portfolio to demonstrate that you can apply malicious and defensive cybersecurity technologies such as file integrity monitors and network scanners. You will be provided with an information system such as a small organisation's network. To prepare the organisation's information system to survive an imminent attack from threat actors, you will:
- Week 3: Perform reconnaissance (12.5%)
- Week 5: Vulnerability detection (12.5%): search the information system for vulnerabilities, analyse Cyber Threat Intelligence (CTI) and prioritise vulnerabilities
- Week 7: Internal attacks (12.5%): implement defenses, develop, run and detect internal attacks
- Week 9: Network attacks (12.5%): implement defenses, develop, run and detect network attacks
Week 3 Friday (28 Mar 2025) 11:45 pm AEST
Feedback for each task be provided within 2 weeks of the due dates. Immediate feedback for some tasks.
You will be marked on aspects such as adherence to cybersecurity standards and frameworks, use of threat intelligence, quality of implementation, configuration and testing scripts and other artefacts including functionality, modularity, style, reuse and documentation, lack of deprecated features, level of automation and use tools.
- Apply cyber security tools to identify vulnerabilities and protect computer systems
- Apply cloud services tools to automate common IT processes and task.
3 Presentation
You will demonstrate the Assignment 2 activities. You will perform reconnaissance, vulnerability detection and run attacks on your information systems and demonstrate the detection, mitigation or protections in action.
Week 11 Friday (30 May 2025) 11:45 pm AEST
Feedback will be returned on the Certification of Grades day.
You will be marked on aspects such as your stage presence and quality of the demonstration including the use of tools to perform reconnaissance, vulnerability detection, attacks and demonstrate detection, mitigation or protections in action.
- Explain cyber security challenges and the technologies available to address those challenges
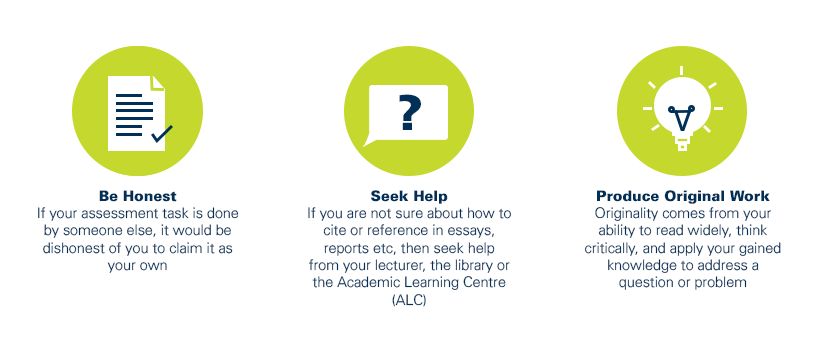
As a CQUniversity student you are expected to act honestly in all aspects of your academic work.
Any assessable work undertaken or submitted for review or assessment must be your own work. Assessable work is any type of work you do to meet the assessment requirements in the unit, including draft work submitted for review and feedback and final work to be assessed.
When you use the ideas, words or data of others in your assessment, you must thoroughly and clearly acknowledge the source of this information by using the correct referencing style for your unit. Using others’ work without proper acknowledgement may be considered a form of intellectual dishonesty.
Participating honestly, respectfully, responsibly, and fairly in your university study ensures the CQUniversity qualification you earn will be valued as a true indication of your individual academic achievement and will continue to receive the respect and recognition it deserves.
As a student, you are responsible for reading and following CQUniversity’s policies, including the Student Academic Integrity Policy and Procedure. This policy sets out CQUniversity’s expectations of you to act with integrity, examples of academic integrity breaches to avoid, the processes used to address alleged breaches of academic integrity, and potential penalties.
What is a breach of academic integrity?
A breach of academic integrity includes but is not limited to plagiarism, self-plagiarism, collusion, cheating, contract cheating, and academic misconduct. The Student Academic Integrity Policy and Procedure defines what these terms mean and gives examples.
Why is academic integrity important?
A breach of academic integrity may result in one or more penalties, including suspension or even expulsion from the University. It can also have negative implications for student visas and future enrolment at CQUniversity or elsewhere. Students who engage in contract cheating also risk being blackmailed by contract cheating services.
Where can I get assistance?
For academic advice and guidance, the Academic Learning Centre (ALC) can support you in becoming confident in completing assessments with integrity and of high standard.
What can you do to act with integrity?